Ransomware is a serious threat to business continuity for healthtech and healthcare companies and compliance with the HIPAA Security Rule. Insurance companies have begun requiring businesses to certify that they have in place components of a ransomware defense such as multi-factor authentication (MFA), security policies and procedures, and business continuity plans. Zero Trust and network microsegmentation are two approaches that are effective against the spread of ransomware and other cybersecurity malicious attacks. These approaches can satisfy liability insurance requirements as well as bolster Electronic Personal Health Information (ePHI) protections.
Vulnerabilities
How do breaches occur that allow for ransomware to enter the enterprise network and compromise ePHI? Trojans and phishing are the most common forms of attack. Trojans act like a legitimate application or file to trick you. It tries to lead you into loading and executing the malware on your device. Once installed, a Trojan can perform the action it was designed for. Email attacks and social engineering are common attacks. Phishing, spear phishing, and business email compromise (BEC) are tactics that work over email. Phishing attacks are a general approach while spear phishing is focused on a specific person. Business email compromise attacks impersonate a person in an employee’s chain of command and seek to have them compromise security. Bring your own devices (BYOD) that are unmanaged are vulnerable. Mobile devices can be especially vulnerable to attacks via SMS messages and vulnerable apps. It is important to protect against attack vectors, minimize the attack surface, and reduce the blast radius for a breach, especially when one has to trade security controls for flexibility.
Cisco’s “2021 Cyber Security Threat Trends (registration required) note that 86% of organizations had at least one user try to connect to a phishing site. Cisco also reports that 50% of organizations encountered ransomware-related activity. Cisco also notes that Healthcare organizations saw higher rates of attacks by Trojans than financial services organizations. Verizon’s “Data Breach Investigations Report (DBIR)” (registration required) notes that the Healthcare sector has seen a shift from breaches caused by internal actors to primarily external actors. 66% of breaches saw personal information compromised, while 55% saw ePHI compromised.
Zero Trust
Zero Trust is a guiding principle that assumes that there is no network edge and access to data, services, systems (and any other corporate assets) are not implicitly trusted solely based on location within your network. A Zero Trust architecture adopts the Zero Trust principle and applies over risk-based compartmentalization of data, relationships between systems and services, business / engineering workflows, and corporate policies. It requires all users and systems to be authenticated and authorized before being granted access to a restricted portion of network, applications, and data. This approach contains the blast radius for a compromised system solely within a compromised system; this is done by enforcing least-privilege access and limiting movement across your network while reducing implicit trust zones. Combined with multi-factor authentication (MFA) and endpoint monitoring, a Zero Trust architecture reduces the likelihood of ransomware spreading from a compromised system; it also limits access to ePHI to only those persons or software programs requiring access.
Microsegmentation
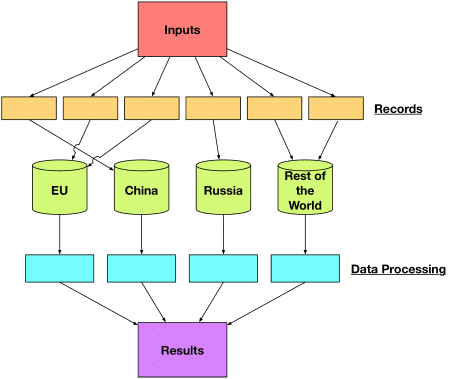
Network microsegmentation divides your internal network into small zones to contain lateral movements. This can be achieved with a combination of network multi-layer access control and boundary protection technologies and identity and the access management (IAM) system. A network microsegment could also encompass various types of physical networks, such as your corporate network, data center, and virtual network in a cloud provider. Access control for a micro-segment dictates both data or system access and the flow of such access at network and application layers. Micro-segmentation should be part of the Zero Trust architecture implementation that contains a breach and prevents further data loss or penetration.
Ten Mile Square Can Help
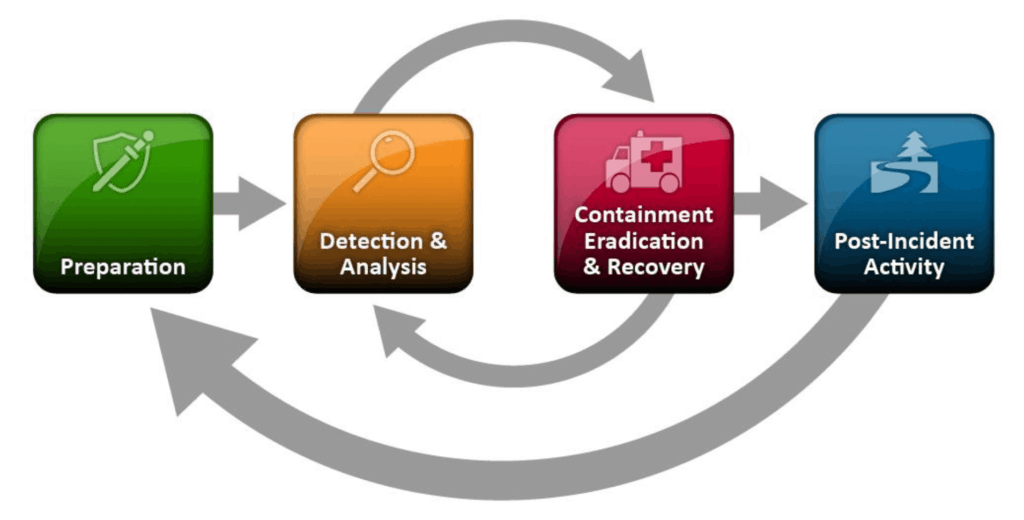
Ten Mile Square works with businesses to ensure their enterprise is protected against cybersecurity threats. We work with you to implement risk-based cybersecurity frameworks and defenses that protect against ransomware and provide compliance with HIPAA. The first step is to assess what assets you have, what the security impact of those assets are, and what gaps in your governance exist. Ten Mile Square offers our Cybersecurity Assessment services for Health Tech and Healthcare companies.