
Embracing a Culture of Data Curation: Unlock the Potential of Untapped Data Wealth
In today’s digital age, data reigns supreme as one of the most valuable assets for businesses across all industries. From
How to establish effective processes and policies to acquire, store, organize, and maintain data. Gain knowledge in how a strong data management system can enable faster responses to market dynamics and customer needs.

In today’s digital age, data reigns supreme as one of the most valuable assets for businesses across all industries. From

One of the many nightmares that keeps management up at night is the thought that, since so much knowledge lives
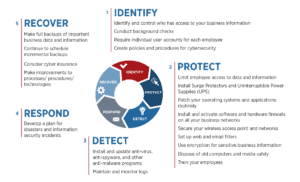
Cybersecurity frameworks provide a structure for managing cybersecurity risk. Companies in financial services, healthcare, and government verticals are required to

Google’s Web Vitals initiative evaluates each of your pages across three critical metrics to arrive at a UX score, which it then
GraphQL was created in 2012 and open-sourced by Facebook in 2015 to relieve issues with the interfaces of the time, particularly for mobile devices with limited or flaky internet connections.
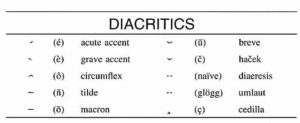
Recently I had the task to find all the Diacritics in a database table. I had to find an easy

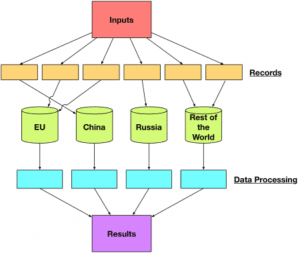
In the previous articles, we discussed the main pieces to consider when designing and implementing an Extract Transform and Load

Let’s say that you have a process that requires a long time to run but you’ve got a limited time

Last week I talked about the need to understand the monetization and commercialization opportunities of your data assets. This week

Are you a data company? If you answered, “No”, you are about to become obsolete. Harsh words perhaps, but that

So as I’m getting my feet on the ground, I thought I’d write a binary classification post for mortals. My
In the last article of the Extract Transform and Load (ETL) series, we talked about how using a canonical object
Overview In the last article in my Extract Transform and Load (ETL) series, Submission Information Packages and High-level Validation, I
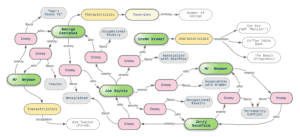
Graph databases are a technology in which the relationships between data are as important as the data itself. Graphs make
The first two major pieces of an Extract Transform and Load pipeline are the Submission Information Package (SIP) and High-level
Part 1 of the Data Ingest Series The process of extract transforms and load (ETL) goes by many names: Data
The XML Schema Definition is a dense document that will take you a lot of time to parse to get
By now you’ve read numerous articles about how the European Union (EU) will enforce its General Data Protection Regulation (GDPR).
Subselects can be used in many ways: filtering, retrieving specific data, and creating custom joins. Writing effective SQL using subselects,
Two popular open source components used in full stack development are Spring and Postgres. Spring gives the developer a plethora
From door to door canvassing to electronic questionnaires, surveys are a tried and true way to collect customer information. There